Create a user with full programmatic access to AWS S3
24 Oct, 2020In this tutorial you’ll learn the following:
- Create a AWS user with only programmatic access
- Create a group and attach a
AmazonS3FullAccesspolicy - Configure and Access S3 using AWS CLI
Requirements:
- AWS CLI
- Access to AWS Console
Install AWS CLI
- To push our content to S3, we need to Install AWS CLI.
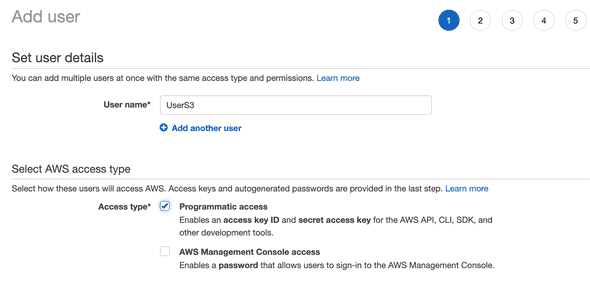
1. Create a AWS user with programmatic access
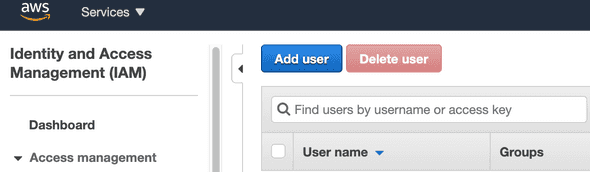
Login to AWS and navigate to Identity access management (IAM)
- Click on
Add user
- Give your user an name and then check the box with
Programmatic access - Next!
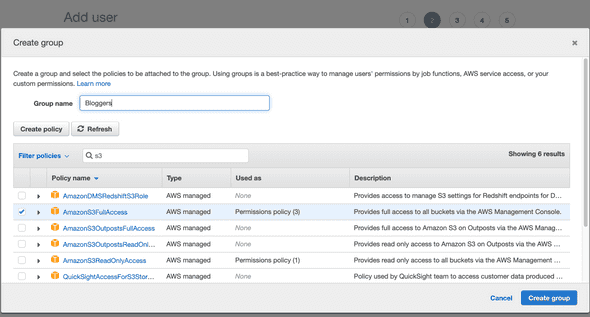
- Create a group and attach a policty, AWS already has a lot of ready made policies, but for our need we will select
AmazonS3FullAccessand this basicly mean that we are allowing any action on any resource related to S3. This is not desired in production as you want to restrict the users access to just the buckets that they work with.
Bear in mind that every user you attach to this group will inherit the permissions with AmazonS3FullAccess.
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Action": "s3:*",
"Resource": "*"
}
]
}- Next!
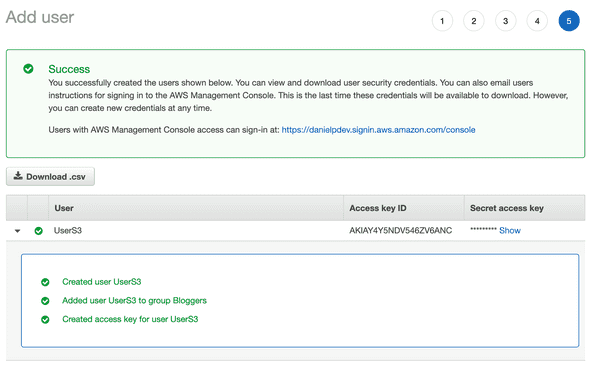
- This is the final step and we have to download the credentials that AWS provided us with.
We will use both Access Key ID and Secret access key to access S3 programmatically.
2. Configure and Access S3 using AWS CLI
Create a file in your home directory .aws/credential and paste:
Access Key IDSecret access key
[default]
aws_access_key_id=AKIAY4Y5NDV5****46ZV6ANC****
aws_secret_access_key=********3. Test to see it working
- Create a S3 bucket
aws s3api create-bucket --bucket my-bucket123131 --region us-east-1
- Output
{
"Location": "/my-bucket123131"
}- List all buckets
aws s3 ls
- Upload files from current directory to a bucket
aws s3 sync . s3://my-bucket123131
- List contents of a particular bucket
aws s3 ls s3://my-bucket123131
- Delete a bucket
aws s3api delete-bucket --bucket my-bucket123131
- Delete a bucket with files using
--forceflag
aws s3 rb s3://my-bucket123131 --force